On occasion I need to use Remote Desktop Protocol (RDP) to access a Windows server that is not directly available on the Internet. For example I might have SSH access to a Linux host on the target network. Or the Windows host has source access controls limiting access to a specific network when I’m traveling. The solution if to setup an SSH tunnel with Putty from my Windows desktop to the “gateway” or “bastion” host and then send the RDP through this tunnel.
So here’s the example parameter:
- RDP is a TCP protocol over port 3389.
- My laptop has a dynamic address.
- The target Windows server has an IP address of 10.10.10.10 and is located on a private network.
- I have a Linux server inside the private network at 10.10.10.5. There’s a port forward on the firewall that allows SSH to the Linux server on the public address 123.123.123.123 on port 22.
To make this work we just need to create a new session profile in Putty. Follow these steps:
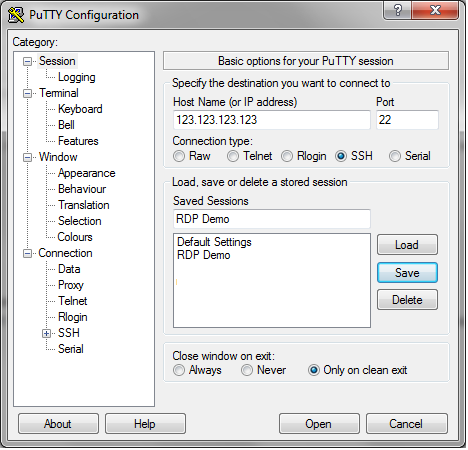
- Start a new Putty session.
- On the session screen: enter the public address of the Linux server (123.123.123.123) and enter a name for the new session profile (RDP Demo).
- Now go to the SSH->Tunnels screen:
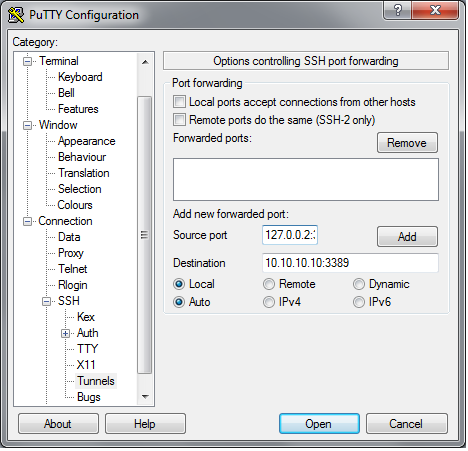
- In the “Source port” field enter the local address that will be forwarded to the remote server. Normally this would be “localhost:3389” but Windows does not like connecting RDP on the loopback interface so we need to use an alternate address of “127.0.0.2:3389”. In the “Destination” field enter the IP address of the Windows server and the port number which is “10.10.10.10:3389” in our example>
- Finally return to the main session screen, click “Save” to save the new profile and then click “Open”.
- An SSH terminal window will open and you’ll be prompted to login to the Linux server. After login, I like to open a ping or run top to keep the session active and avoid timeouts on any firewalls. At this point, Putty, in cooperation with the SSH daemon on the Linux server, packets sent to 127.0.0.2:3389 will be tunneled over the SSH connection and resent on the remote network to 10.10.10.10:3389.
- Now just open your Remote Desktop client and enter “127.0.0.2:3389” as the remote address.
This same technique can be used to tunnel other traffic, just adjust the port numbers as needed.