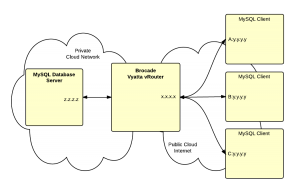
This article demonstrates how to configure a Vyatta firewall to allow incoming requests from a group of clients to an internal MySQL server.
Assuming that you have three external MySQL clients with IPv4 addresses:
[A:y.y.y.y]
[B:y.y.y.y]
[C:y.y.y.y]
We’ll put these addresses in a group called [clientgroup]. You can name the group appropriately for your installation.
The external address of the firewall is [x.x.x.x] and the internal address of the MySQL server is [z.z.z.z].
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 |
# enter config mode config # create address group set firewall group address-group [clientgroup] address [A:y.y.y.y] set firewall group address-group [clientgroup] address [B:y.y.y.y] set firewall group address-group [clientgroup] address [C:y.y.y.y] # select "untrusted" firewall - this it firewall rule set that controls # traffic passing through the device edit firewall name untrusted # allow the mysql traffic from the source address group set rule 505 action accept set rule 505 destination port '3306' set rule 505 protocol 'tcp' set rule 505 source group address-group [clientgroup] # add nat rules set nat destination rule 15 inbound-interface eth0 set nat destination rule 15 destination address [x.x.x.x] set nat destination rule 15 destination port mysql set nat destination rule 15 protocol tcp set nat destination rule 15 translation address [z.z.z.z] |